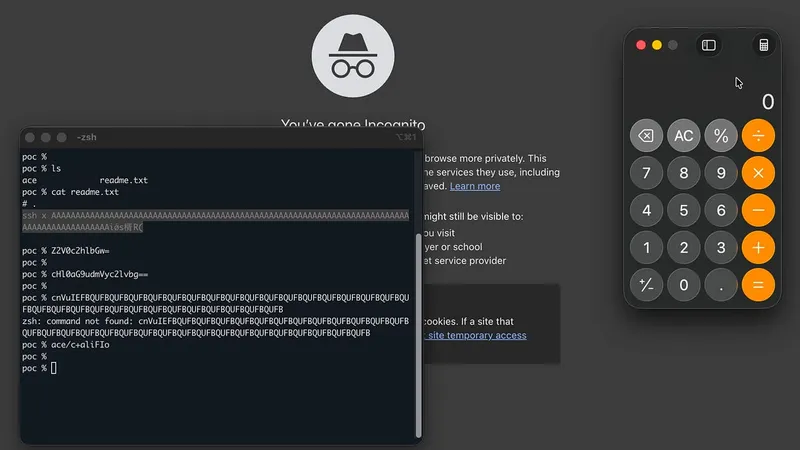
Even "cat readme.txt" is not safe
Using iTerm2, executing the command "cat readme.txt" can lead to arbitrary code execution. This vulnerability arises from iTerm2's legitimate features that inadvertently allow such exploits.
blog.calif.io
5 min
4/17/2026
Let's discuss sandbox isolation
Sandboxing untrusted code is crucial for safely running AI-generated code, customer scripts on multi-tenant platforms, and RL training pipelines. Various technologies, including Docker containers, microVMs, and WebAssembly modules, provide different levels of isolation for executing potentially harmful code.
shayon.dev
19 min
2/27/2026
Even "cat readme.txt" is not safe
Using iTerm2, executing the command "cat readme.txt" can lead to arbitrary code execution. This vulnerability arises from iTerm2's legitimate features that inadvertently allow such exploits.
blog.calif.io
5 min
4/17/2026
Let's discuss sandbox isolation
Sandboxing untrusted code is crucial for safely running AI-generated code, customer scripts on multi-tenant platforms, and RL training pipelines. Various technologies, including Docker containers, microVMs, and WebAssembly modules, provide different levels of isolation for executing potentially harmful code.
shayon.dev
19 min
2/27/2026
Even "cat readme.txt" is not safe
Using iTerm2, executing the command "cat readme.txt" can lead to arbitrary code execution. This vulnerability arises from iTerm2's legitimate features that inadvertently allow such exploits.
blog.calif.io
5 min
4/17/2026
Let's discuss sandbox isolation
Sandboxing untrusted code is crucial for safely running AI-generated code, customer scripts on multi-tenant platforms, and RL training pipelines. Various technologies, including Docker containers, microVMs, and WebAssembly modules, provide different levels of isolation for executing potentially harmful code.
shayon.dev
19 min
2/27/2026
No more articles to load