Incident Report: CVE-2024-YIKES
CVE-2024-YIKES outlines a series of vulnerabilities that led to significant security incidents. The report details the technical specifics of the vulnerabilities and their impact on affected systems.
nesbitt.io
1 min
3d ago
Securing a DoD contractor: Finding a multi-tenant authorization vulnerability
A multi-tenant authorization vulnerability was discovered in a Department of Defense contractor, leading to zero tenant isolation and exposure of military training data. The responsible disclosure process took five months to complete.
strix.ai
1 min
5/4/2026
After dissing Anthropic for limiting Mythos, OpenAI restricts access to Cyber
OpenAI will restrict access to its cybersecurity tool, Cyber, rolling it out initially to "critical cyber defenders." Interested users must submit their credentials and intended use through an application on OpenAI's website to gain access.
techcrunch.com
1 min
5/1/2026
CPanel and WHM Authentication Bypass – CVE-2026-41940
cPanel and WHM are vulnerable to an authentication bypass exploit identified as CVE-2026-41940. This vulnerability could allow unauthorized access to affected systems, posing significant security risks.
labs.watchtowr.com
18 min
4/30/2026
Copy Fail – CVE-2026-31431
Copy Fail is a logic flaw that allows for local privilege escalation on Linux systems without the need for a race window or kernel-specific offsets. A 732-byte Python script can exploit this flaw to gain root access on every Linux distribution released since 2017, functioning unmodified across multiple systems.
copy.fail
3 min
4/29/2026
Cybersec is a thankless job: expanding workload and shrinking pay packet
Seventy-one percent of cybersecurity professionals experienced stagnant wages last year despite increased workloads and responsibilities. In the UK, 77 percent of security staff saw no salary increase in 2025, reflecting a global trend in the industry.
theregister.com
3 min
4/28/2026
Three men are facing charges in Toronto SMS Blaster arrests
Three men in Toronto have been arrested and charged in connection with an SMS blaster operation. The arrests are part of a crackdown on illegal mass messaging activities.
tps.ca
1 min
4/27/2026
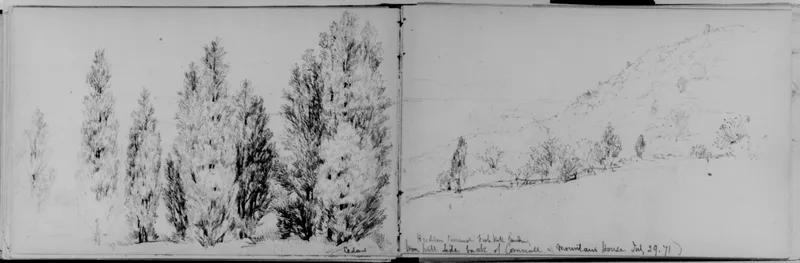
4TB of voice samples just stolen from 40k AI contractors at Mercor
4TB of voice samples from 40,000 AI contractors were stolen and posted by the extortion group Lapsus$ on April 4, 2026. The leaked data includes voice biometrics linked to government-issued identity documents, raising concerns about potential misuse.
app.oravys.com
6 min
4/27/2026
Claude Mythos AI unauthorised access claim probed by Anthropic
Anthropic is investigating a claim of unauthorized access to its Claude Mythos AI tool, which is described as too powerful for public release. The investigation was prompted by a report indicating that a small group accessed the tool through a third-party vendor environment.
bbc.com
3 min
4/22/2026
Vercel Says Internal Systems Hit in Breach
Vercel reported a breach of its internal systems and has engaged an incident response provider to investigate the intrusion. Specific details regarding the breach remain limited.
decipher.sc
2 min
4/19/2026
Incident Report: CVE-2024-YIKES
CVE-2024-YIKES outlines a series of vulnerabilities that led to significant security incidents. The report details the technical specifics of the vulnerabilities and their impact on affected systems.
nesbitt.io
1 min
3d ago
After dissing Anthropic for limiting Mythos, OpenAI restricts access to Cyber
OpenAI will restrict access to its cybersecurity tool, Cyber, rolling it out initially to "critical cyber defenders." Interested users must submit their credentials and intended use through an application on OpenAI's website to gain access.
techcrunch.com
1 min
5/1/2026
Copy Fail – CVE-2026-31431
Copy Fail is a logic flaw that allows for local privilege escalation on Linux systems without the need for a race window or kernel-specific offsets. A 732-byte Python script can exploit this flaw to gain root access on every Linux distribution released since 2017, functioning unmodified across multiple systems.
copy.fail
3 min
4/29/2026
Three men are facing charges in Toronto SMS Blaster arrests
Three men in Toronto have been arrested and charged in connection with an SMS blaster operation. The arrests are part of a crackdown on illegal mass messaging activities.
tps.ca
1 min
4/27/2026
Claude Mythos AI unauthorised access claim probed by Anthropic
Anthropic is investigating a claim of unauthorized access to its Claude Mythos AI tool, which is described as too powerful for public release. The investigation was prompted by a report indicating that a small group accessed the tool through a third-party vendor environment.
bbc.com
3 min
4/22/2026
Securing a DoD contractor: Finding a multi-tenant authorization vulnerability
A multi-tenant authorization vulnerability was discovered in a Department of Defense contractor, leading to zero tenant isolation and exposure of military training data. The responsible disclosure process took five months to complete.
strix.ai
1 min
5/4/2026
CPanel and WHM Authentication Bypass – CVE-2026-41940
cPanel and WHM are vulnerable to an authentication bypass exploit identified as CVE-2026-41940. This vulnerability could allow unauthorized access to affected systems, posing significant security risks.
labs.watchtowr.com
18 min
4/30/2026
Cybersec is a thankless job: expanding workload and shrinking pay packet
Seventy-one percent of cybersecurity professionals experienced stagnant wages last year despite increased workloads and responsibilities. In the UK, 77 percent of security staff saw no salary increase in 2025, reflecting a global trend in the industry.
theregister.com
3 min
4/28/2026
4TB of voice samples just stolen from 40k AI contractors at Mercor
4TB of voice samples from 40,000 AI contractors were stolen and posted by the extortion group Lapsus$ on April 4, 2026. The leaked data includes voice biometrics linked to government-issued identity documents, raising concerns about potential misuse.
app.oravys.com
6 min
4/27/2026
Vercel Says Internal Systems Hit in Breach
Vercel reported a breach of its internal systems and has engaged an incident response provider to investigate the intrusion. Specific details regarding the breach remain limited.
decipher.sc
2 min
4/19/2026
Incident Report: CVE-2024-YIKES
CVE-2024-YIKES outlines a series of vulnerabilities that led to significant security incidents. The report details the technical specifics of the vulnerabilities and their impact on affected systems.
nesbitt.io
1 min
3d ago
CPanel and WHM Authentication Bypass – CVE-2026-41940
cPanel and WHM are vulnerable to an authentication bypass exploit identified as CVE-2026-41940. This vulnerability could allow unauthorized access to affected systems, posing significant security risks.
labs.watchtowr.com
18 min
4/30/2026
Three men are facing charges in Toronto SMS Blaster arrests
Three men in Toronto have been arrested and charged in connection with an SMS blaster operation. The arrests are part of a crackdown on illegal mass messaging activities.
tps.ca
1 min
4/27/2026
Vercel Says Internal Systems Hit in Breach
Vercel reported a breach of its internal systems and has engaged an incident response provider to investigate the intrusion. Specific details regarding the breach remain limited.
decipher.sc
2 min
4/19/2026
Securing a DoD contractor: Finding a multi-tenant authorization vulnerability
A multi-tenant authorization vulnerability was discovered in a Department of Defense contractor, leading to zero tenant isolation and exposure of military training data. The responsible disclosure process took five months to complete.
strix.ai
1 min
5/4/2026
Copy Fail – CVE-2026-31431
Copy Fail is a logic flaw that allows for local privilege escalation on Linux systems without the need for a race window or kernel-specific offsets. A 732-byte Python script can exploit this flaw to gain root access on every Linux distribution released since 2017, functioning unmodified across multiple systems.
copy.fail
3 min
4/29/2026
4TB of voice samples just stolen from 40k AI contractors at Mercor
4TB of voice samples from 40,000 AI contractors were stolen and posted by the extortion group Lapsus$ on April 4, 2026. The leaked data includes voice biometrics linked to government-issued identity documents, raising concerns about potential misuse.
app.oravys.com
6 min
4/27/2026
After dissing Anthropic for limiting Mythos, OpenAI restricts access to Cyber
OpenAI will restrict access to its cybersecurity tool, Cyber, rolling it out initially to "critical cyber defenders." Interested users must submit their credentials and intended use through an application on OpenAI's website to gain access.
techcrunch.com
1 min
5/1/2026
Cybersec is a thankless job: expanding workload and shrinking pay packet
Seventy-one percent of cybersecurity professionals experienced stagnant wages last year despite increased workloads and responsibilities. In the UK, 77 percent of security staff saw no salary increase in 2025, reflecting a global trend in the industry.
theregister.com
3 min
4/28/2026
Claude Mythos AI unauthorised access claim probed by Anthropic
Anthropic is investigating a claim of unauthorized access to its Claude Mythos AI tool, which is described as too powerful for public release. The investigation was prompted by a report indicating that a small group accessed the tool through a third-party vendor environment.
bbc.com
3 min
4/22/2026