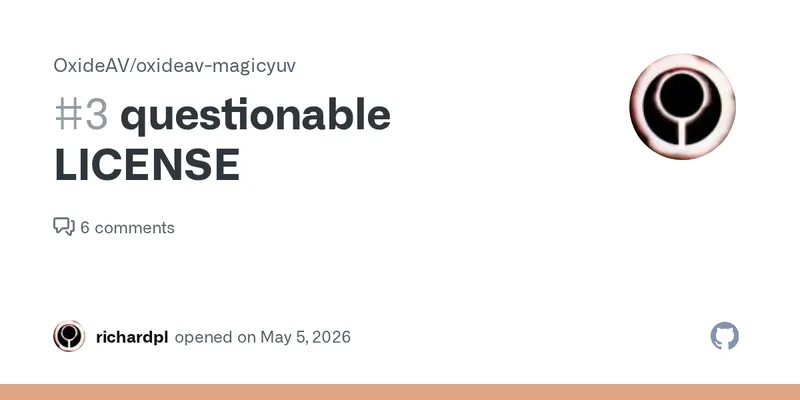
FFmpeg developer calls out OxideAV for AI license laundering of his code
The issue discusses the location of the file docs/video/magicyuv/magicyuv-trace-reverse-engineering.md within the OxideAV repository. Users are seeking clarification on the licensing and access of this specific document.
github.com
1 min
5/6/2026
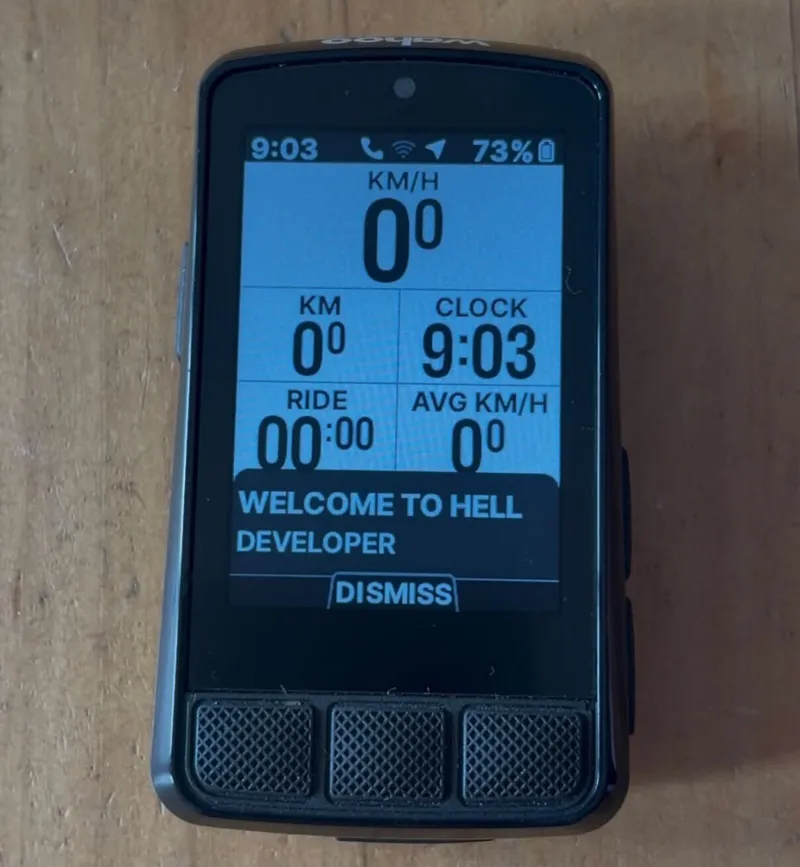
Welcome to Hell Developer
A Wahoo ELEMNT Bolt v3 cycling computer stopped syncing rides to its companion app, prompting reverse engineering of Bluetooth packets and decompiling an Android APK. This process revealed a hidden debug mode, indicated by the message “WELCOME TO HELL DEVELOPER.”
noahclements.com
5 min
5/2/2026
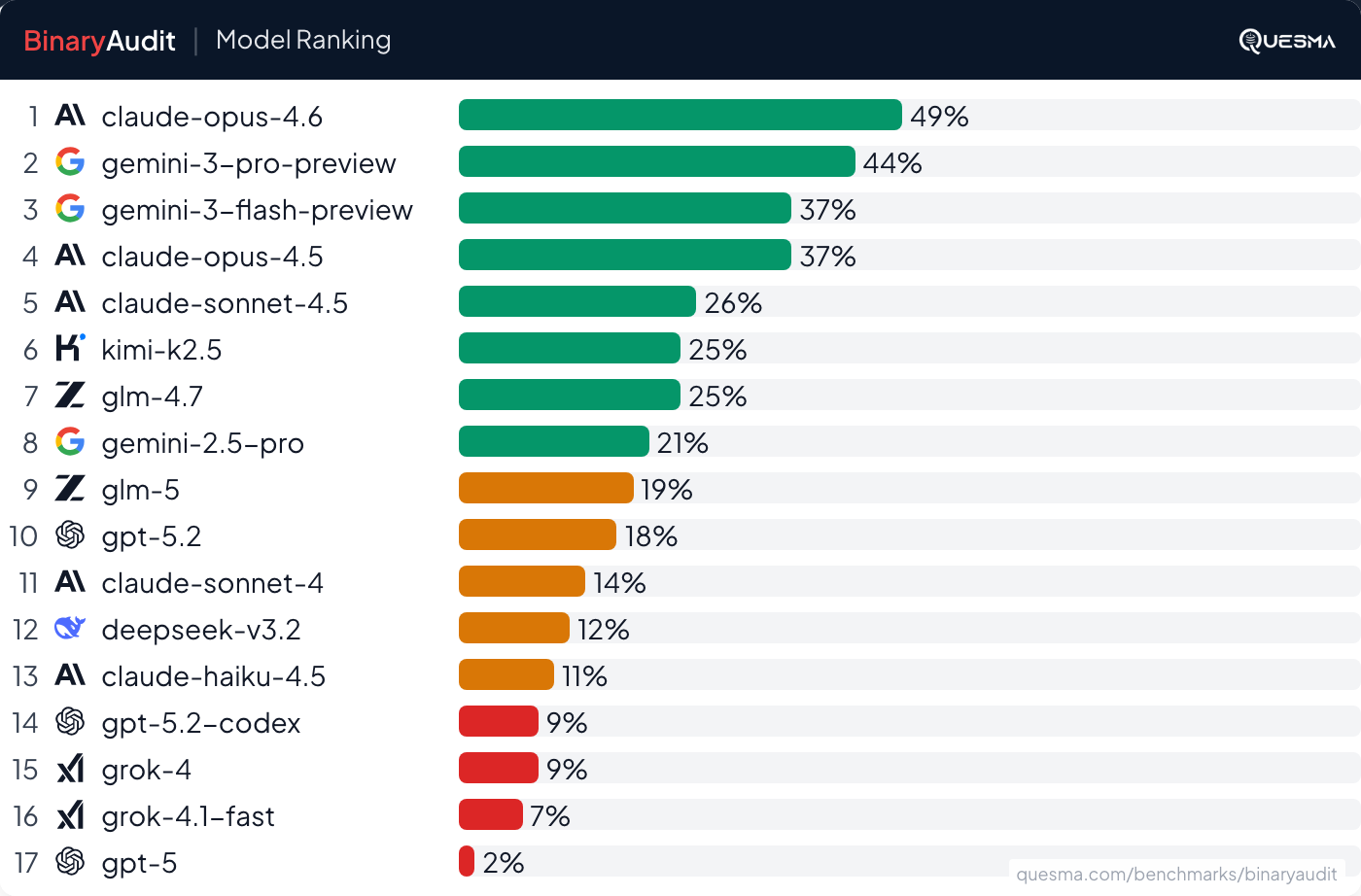
We hid backdoors in ~40MB binaries and asked AI + Ghidra to find them
Backdoors were hidden in ~40MB binaries to test AI and Ghidra's capabilities in malware detection. The experiment involved collaboration with Michał “Redford” Kowalczyk, a reverse engineering expert, to establish a benchmark for identifying malicious code in binaries.
quesma.com
14 min
2/22/2026
FFmpeg developer calls out OxideAV for AI license laundering of his code
The issue discusses the location of the file docs/video/magicyuv/magicyuv-trace-reverse-engineering.md within the OxideAV repository. Users are seeking clarification on the licensing and access of this specific document.
github.com
1 min
5/6/2026
We hid backdoors in ~40MB binaries and asked AI + Ghidra to find them
Backdoors were hidden in ~40MB binaries to test AI and Ghidra's capabilities in malware detection. The experiment involved collaboration with Michał “Redford” Kowalczyk, a reverse engineering expert, to establish a benchmark for identifying malicious code in binaries.
quesma.com
14 min
2/22/2026
Welcome to Hell Developer
A Wahoo ELEMNT Bolt v3 cycling computer stopped syncing rides to its companion app, prompting reverse engineering of Bluetooth packets and decompiling an Android APK. This process revealed a hidden debug mode, indicated by the message “WELCOME TO HELL DEVELOPER.”
noahclements.com
5 min
5/2/2026
FFmpeg developer calls out OxideAV for AI license laundering of his code
The issue discusses the location of the file docs/video/magicyuv/magicyuv-trace-reverse-engineering.md within the OxideAV repository. Users are seeking clarification on the licensing and access of this specific document.
github.com
1 min
5/6/2026
Welcome to Hell Developer
A Wahoo ELEMNT Bolt v3 cycling computer stopped syncing rides to its companion app, prompting reverse engineering of Bluetooth packets and decompiling an Android APK. This process revealed a hidden debug mode, indicated by the message “WELCOME TO HELL DEVELOPER.”
noahclements.com
5 min
5/2/2026
We hid backdoors in ~40MB binaries and asked AI + Ghidra to find them
Backdoors were hidden in ~40MB binaries to test AI and Ghidra's capabilities in malware detection. The experiment involved collaboration with Michał “Redford” Kowalczyk, a reverse engineering expert, to establish a benchmark for identifying malicious code in binaries.
quesma.com
14 min
2/22/2026
No more articles to load