The woes of sanitizing SVGs
muffin.ink
April 27, 2026
13 min read
🔥🔥🔥🔥🔥
49/100
Summary
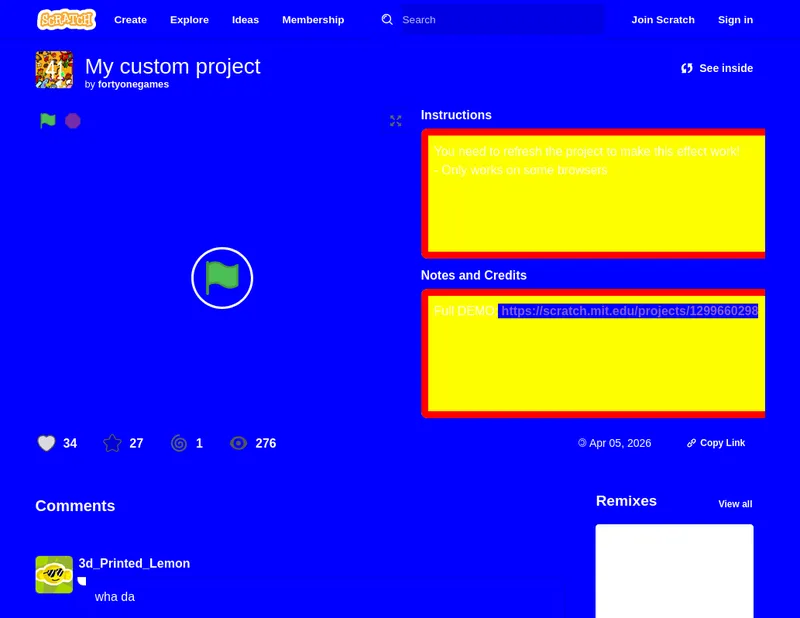
Scratch has a history of SVG-related vulnerabilities due to the parsing of user-generated content into an <svg> element, which is appended to the main document. This operation poses inherent security risks, leading Scratch to implement increasingly complex sanitization methods.
Key Takeaways
- Scratch has a history of SVG-related vulnerabilities due to parsing user-generated content into an <svg> element, which poses security risks.
- In 2019, Scratch addressed an XSS vulnerability caused by <script> tags in SVGs by using a regular expression to remove them.
- Subsequent vulnerabilities in 2020 and 2022 revealed that previous fixes were inadequate, allowing XSS attacks and HTTP leaks through various methods.
- As of 2023, Scratch continues to face challenges with SVG sanitization, indicating that its current approach may be insufficient for ensuring security.
Community Sentiment
Positives
- The article highlights the importance of Content Security Policy (CSP) as a credible solution for addressing HTTP leak problems, which is crucial for enhancing web security.
- The suggestion of a sandbox attribute for inline SVG tags could significantly improve security by restricting dynamic content, though it may face browser support challenges.
Concerns
- The lack of an industry standard for SVG sanitization hampers usability, as users cannot guarantee compatibility across different tools and browsers.
- Relying on regular expressions for sanitizing SVGs is problematic, as it can lead to security vulnerabilities and does not address the complexity of SVG content.