Claude Wrote a Full FreeBSD Remote Kernel RCE with Root Shell (CVE-2026-4747)
github.com
April 1, 2026
14 min read
🔥🔥🔥🔥🔥
61/100
Summary
CVE-2026-4747 affects FreeBSD versions 13.5, 14.3, 14.4, and 15.0, specifically when the NFS server with kgssapi.ko loaded is utilized. The vulnerability arises in the svc_rpc_gss_validate() function, which improperly reconstructs an RPC header into a 128-byte stack buffer for GSS-API signature verification.
Key Takeaways
- CVE-2026-4747 is a vulnerability in FreeBSD affecting versions 13.5, 14.3, 14.4, and 15.0, specifically in the kgssapi module used for RPCSEC_GSS authentication.
- The vulnerability allows for a stack buffer overflow due to a lack of bounds checking on the length of the RPCSEC_GSS credential body, potentially leading to remote kernel code execution.
- A patch has been implemented to add a bounds check before copying the credential body into the stack buffer to prevent overflow.
- The NFS server, which uses the vulnerable kgssapi module, listens on port 2049/TCP and processes RPC packets in kernel context, making the vulnerability exploitable over the network.
Community Sentiment
Positives
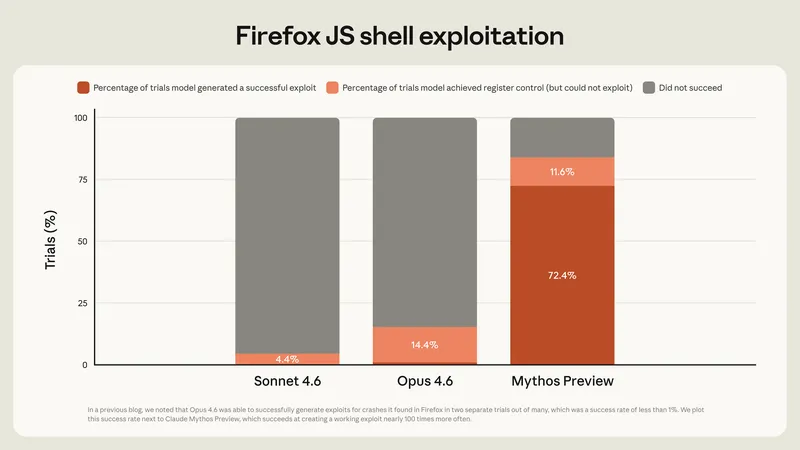
- The ability of Claude to generate a full exploit demonstrates the growing capabilities of LLMs in understanding and manipulating complex systems, which could have significant implications for cybersecurity.
Concerns
- Claude did not independently discover the vulnerability, raising concerns about the reliance on AI for proactive security measures rather than reactive ones.
- The lack of KASLR in FreeBSD 14.x highlights potential weaknesses in its security architecture, which could be exploited by AI-generated exploits.