Copy Fail – CVE-2026-31431

copy.fail
April 29, 2026
3 min read
🔥🔥🔥🔥🔥
67/100
Summary
Copy Fail is a logic flaw that allows for local privilege escalation on Linux systems without the need for a race window or kernel-specific offsets. A 732-byte Python script can exploit this flaw to gain root access on every Linux distribution released since 2017, functioning unmodified across multiple systems.
Key Takeaways
- Copy Fail is a Linux local privilege escalation vulnerability that exploits a logic flaw, allowing unprivileged users to gain root access on any Linux distribution shipped since 2017 using a 732-byte Python script.
- The exploit is silently exploitable for nearly a decade and requires no network access or special kernel debugging features, making it a significant risk for shared environments.
- A patch is available that reverts a specific in-place optimization in the kernel, and users are advised to disable the algif_aead module before applying the patch.
- The vulnerability affects multiple Linux distributions, including Ubuntu, Amazon Linux, RHEL, and SUSE, and can compromise shared systems such as CI/CD environments and multi-user servers.
Community Sentiment
Positives
- The vulnerability appears to be real and poses a high risk, prompting necessary security updates across affected systems.
- The discovery of this vulnerability contributes meaningfully to the open-source software ecosystem, highlighting the importance of security in AI applications.
Concerns
- Claims of the exploit escaping containers lack supporting evidence, raising doubts about its effectiveness in real-world scenarios.
- The assertion that the script roots every Linux distribution since 2017 is misleading, as it has only been tested on a few and fails on others like Alpine.
- The vulnerability is being treated as a medium risk by many distros, despite its potential for local root privilege escalation, which should be prioritized higher.
Related Articles
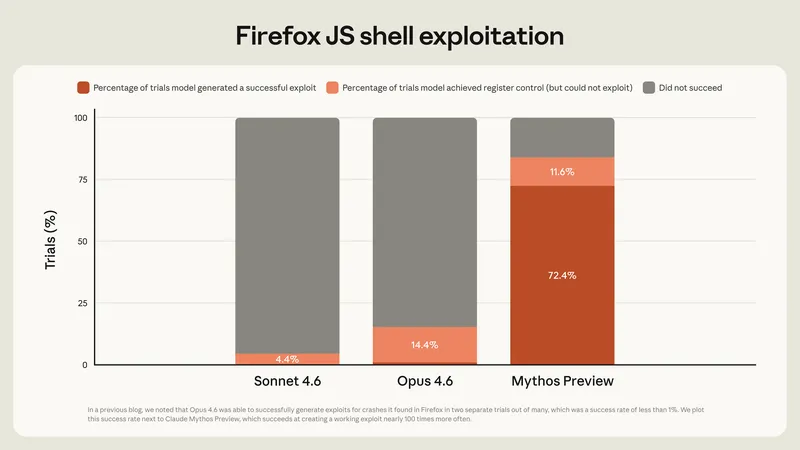
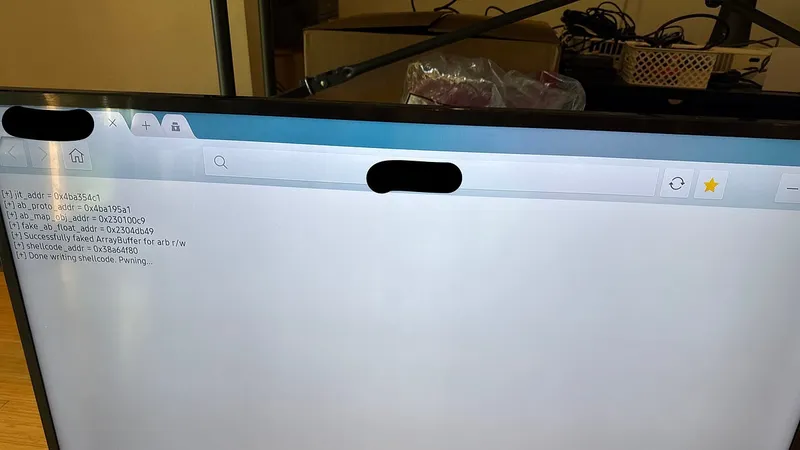
Assessing Claude Mythos Preview's cybersecurity capabilities
Apr 7, 2026
Codex Hacked a Samsung TV
Apr 16, 2026
Claude Code Found a Linux Vulnerability Hidden for 23 Years
Apr 3, 2026
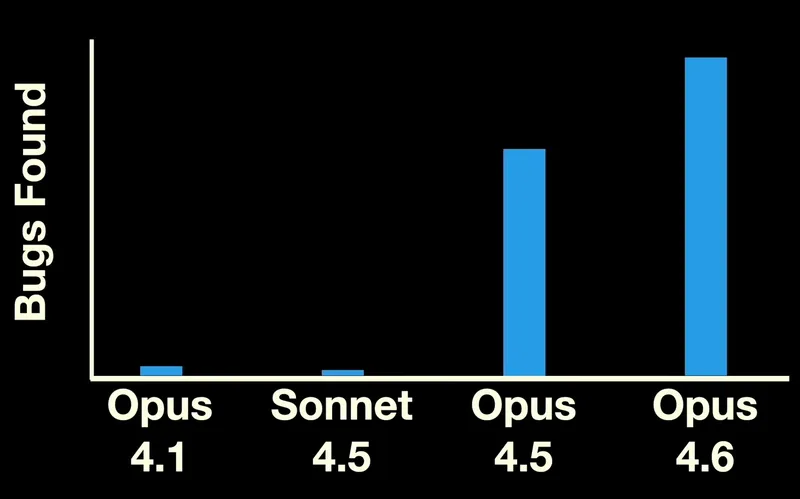
We reproduced Anthropic's Mythos findings with public models
Apr 17, 2026
Claude Wrote a Full FreeBSD Remote Kernel RCE with Root Shell (CVE-2026-4747)
Apr 1, 2026