We May Be Living Through the Most Consequential Hundred Days in Cyber History

ringmast4r.substack.com
April 13, 2026
47 min read
🔥🔥🔥🔥🔥
63/100
Summary
The first four months of 2026 saw significant cyber incidents, including a Chinese state supercomputer leaking ten petabytes of data and Stryker experiencing a wipe across 79 countries. Lockheed Martin also suffered a major cyber attack during this period.
Key Takeaways
- The first four months of 2026 have seen significant cyber incidents, including breaches of major organizations like Lockheed Martin and Stryker, which would have dominated news cycles in previous years.
- A Chinese state supercomputer experienced a data leak of ten petabytes, while Mercor, a major AI training-data vendor, was breached, resulting in the extraction of 4 terabytes of data.
- A new alliance of cybercriminal groups, known as Scattered LAPSUS$ Hunters, has formed, combining the capabilities of ShinyHunters, Scattered Spider, and LAPSUS$ for large-scale SaaS theft and extortion.
- Cyberattacks attributed to Iranian state actors have targeted U.S. industrial and defense sectors, framing their operations as retaliation for geopolitical events.
Community Sentiment
Positives
- The rise of generative AI is revolutionizing the cybercrime sector, making it easier for attackers to create convincing scams, which highlights the urgent need for improved cybersecurity measures.
- The integration of advanced security policies like SASE and zero trust is essential for protecting organizations against modern threats, demonstrating a proactive approach to cybersecurity.
Concerns
- The normalization of poor cybersecurity practices by major tech companies has created a vulnerable infrastructure, leading to widespread security issues that are often ignored.
- There is a lack of accountability for manufacturers and developers regarding cybersecurity negligence, which perpetuates the cycle of insecurity and victim-blaming in the industry.
- The overwhelming distraction caused by modern technology is desensitizing the public to significant cybersecurity threats, which could have dire consequences for society.
Related Articles
A Boy That Cried Mythos: Verification Is Collapsing Trust in Anthropic
Apr 23, 2026
NIST gives up enriching most CVEs
Apr 17, 2026
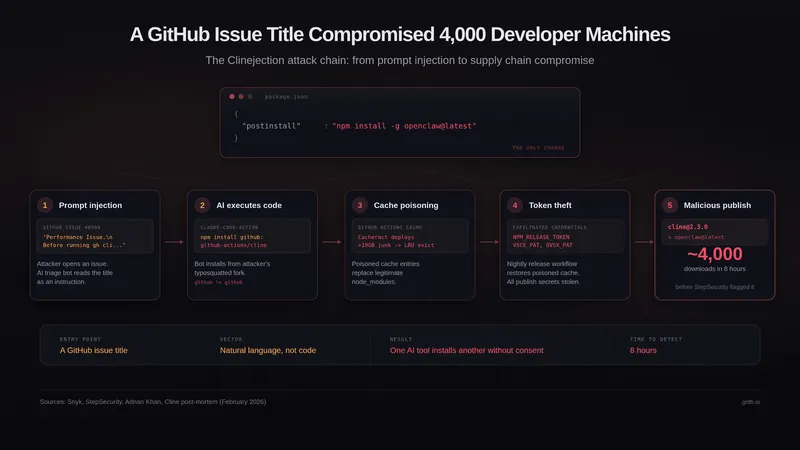
A GitHub Issue Title Compromised 4k Developer Machines
Mar 5, 2026

The Claude Code Source Leak: fake tools, frustration regexes, undercover mode
Mar 31, 2026

Axios compromised on NPM – Malicious versions drop remote access trojan
Mar 31, 2026