Axios compromised on NPM – Malicious versions drop remote access trojan

stepsecurity.io
March 31, 2026
17 min read
82/100
Summary
Two malicious versions of the axios HTTP client library, axios@1.14.1 and axios@0.30.4, were published to npm using compromised credentials of a lead maintainer. The attacker altered the maintainer's email to a ProtonMail address and manually published the malicious packages, which included a remote access Trojan.
Key Takeaways
- Two malicious versions of the axios library, axios@1.14.1 and axios@0.30.4, were published to npm using compromised credentials of a lead maintainer, allowing the attacker to bypass normal security protocols.
- The malicious packages inject a fake dependency, plain-crypto-js@4.2.1, which executes a postinstall script that acts as a cross-platform remote access trojan (RAT) dropper targeting macOS, Windows, and Linux.
- The attack was pre-staged over 18 hours, with the malicious dependency seeded on npm before the axios releases to avoid detection by security scanners.
- Developers who installed axios@1.14.1 or axios@0.30.4 should assume their systems are compromised due to the sophisticated nature of the supply chain attack.
Community Sentiment
Positives
- The introduction of minimum release age settings in npm, bun, and pnpm can significantly enhance package security by preventing the immediate installation of potentially harmful updates.
Concerns
- The compromise of Axios highlights a critical vulnerability in package management systems, raising concerns about the safety and reliability of widely-used dependencies.
- There is a growing anxiety among developers about the security of package managers, with fears that similar incidents could occur in other ecosystems like Rust.
- The reliance on untrusted dependencies in projects creates a significant risk, leading to a lack of confidence in using popular programming languages like Python and Node.js.
Related Articles
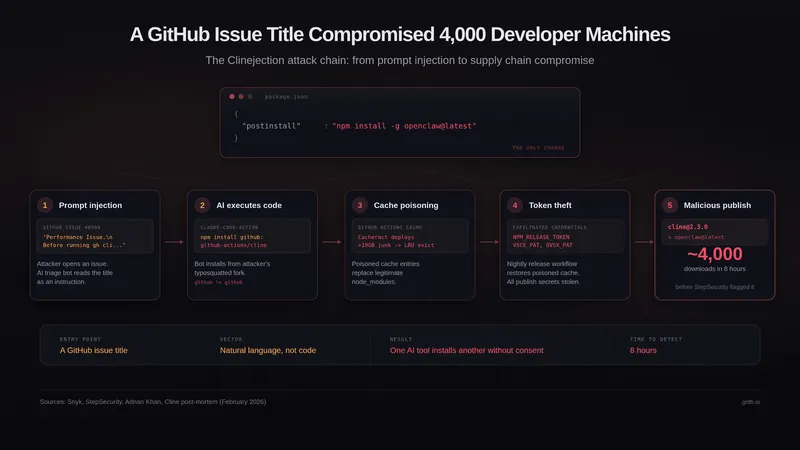
A GitHub Issue Title Compromised 4k Developer Machines
Mar 5, 2026
Shai-Hulud Themed Malware Found in the PyTorch Lightning AI Training Library
Apr 30, 2026

We May Be Living Through the Most Consequential Hundred Days in Cyber History
Apr 13, 2026

Notepad++ supply chain attack breakdown
Feb 3, 2026
Glassworm Is Back: A New Wave of Invisible Unicode Attacks Hits Repositories
Mar 15, 2026