Google says criminal hackers used AI to find a major software flaw
Criminal hackers utilized artificial intelligence to identify a previously unknown software flaw, marking the first instance of AI being used in this manner. Google reported that this attempted cyberattack indicates potential future threats in cybersecurity.
nytimes.com
1 min
2d ago
Copy Fail – CVE-2026-31431
Copy Fail is a logic flaw that allows for local privilege escalation on Linux systems without the need for a race window or kernel-specific offsets. A 732-byte Python script can exploit this flaw to gain root access on every Linux distribution released since 2017, functioning unmodified across multiple systems.
copy.fail
3 min
4/29/2026
Supply chain nightmare: How Rust will be attacked and what we can do to mitigate
Rust is vulnerable to supply chain attacks due to its reliance on third-party crates and libraries. Mitigation strategies include improving dependency management and enhancing security practices within the Rust ecosystem.
kerkour.com
1 min
4/10/2026
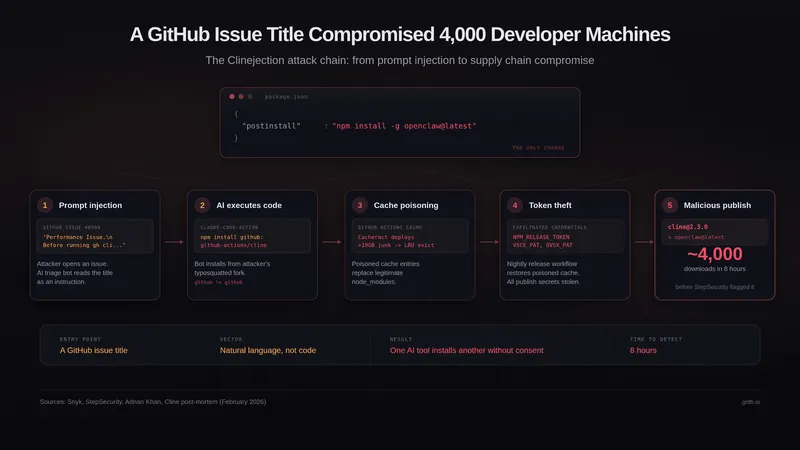
A GitHub Issue Title Compromised 4k Developer Machines
On February 17, 2026, a malicious version of the Cline package was published to npm, which included a code change in the package.json file that executed a post-install command to install OpenClaw, an AI agent with full system access. This led to approximately 4,000 developer machines being compromised as users installed or updated the Cline package without consent.
grith.ai
6 min
3/5/2026
Making frontier cybersecurity capabilities available to defenders
Claude Code Security is a new capability in Claude Code that scans codebases for security vulnerabilities and suggests targeted software patches for human review. It aims to assist security teams in addressing the overwhelming number of software vulnerabilities.
anthropic.com
4 min
2/20/2026
Google says criminal hackers used AI to find a major software flaw
Criminal hackers utilized artificial intelligence to identify a previously unknown software flaw, marking the first instance of AI being used in this manner. Google reported that this attempted cyberattack indicates potential future threats in cybersecurity.
nytimes.com
1 min
2d ago
Supply chain nightmare: How Rust will be attacked and what we can do to mitigate
Rust is vulnerable to supply chain attacks due to its reliance on third-party crates and libraries. Mitigation strategies include improving dependency management and enhancing security practices within the Rust ecosystem.
kerkour.com
1 min
4/10/2026
Making frontier cybersecurity capabilities available to defenders
Claude Code Security is a new capability in Claude Code that scans codebases for security vulnerabilities and suggests targeted software patches for human review. It aims to assist security teams in addressing the overwhelming number of software vulnerabilities.
anthropic.com
4 min
2/20/2026
Copy Fail – CVE-2026-31431
Copy Fail is a logic flaw that allows for local privilege escalation on Linux systems without the need for a race window or kernel-specific offsets. A 732-byte Python script can exploit this flaw to gain root access on every Linux distribution released since 2017, functioning unmodified across multiple systems.
copy.fail
3 min
4/29/2026
A GitHub Issue Title Compromised 4k Developer Machines
On February 17, 2026, a malicious version of the Cline package was published to npm, which included a code change in the package.json file that executed a post-install command to install OpenClaw, an AI agent with full system access. This led to approximately 4,000 developer machines being compromised as users installed or updated the Cline package without consent.
grith.ai
6 min
3/5/2026
Google says criminal hackers used AI to find a major software flaw
Criminal hackers utilized artificial intelligence to identify a previously unknown software flaw, marking the first instance of AI being used in this manner. Google reported that this attempted cyberattack indicates potential future threats in cybersecurity.
nytimes.com
1 min
2d ago
A GitHub Issue Title Compromised 4k Developer Machines
On February 17, 2026, a malicious version of the Cline package was published to npm, which included a code change in the package.json file that executed a post-install command to install OpenClaw, an AI agent with full system access. This led to approximately 4,000 developer machines being compromised as users installed or updated the Cline package without consent.
grith.ai
6 min
3/5/2026
Copy Fail – CVE-2026-31431
Copy Fail is a logic flaw that allows for local privilege escalation on Linux systems without the need for a race window or kernel-specific offsets. A 732-byte Python script can exploit this flaw to gain root access on every Linux distribution released since 2017, functioning unmodified across multiple systems.
copy.fail
3 min
4/29/2026
Making frontier cybersecurity capabilities available to defenders
Claude Code Security is a new capability in Claude Code that scans codebases for security vulnerabilities and suggests targeted software patches for human review. It aims to assist security teams in addressing the overwhelming number of software vulnerabilities.
anthropic.com
4 min
2/20/2026
Supply chain nightmare: How Rust will be attacked and what we can do to mitigate
Rust is vulnerable to supply chain attacks due to its reliance on third-party crates and libraries. Mitigation strategies include improving dependency management and enhancing security practices within the Rust ecosystem.
kerkour.com
1 min
4/10/2026
No more articles to load