GitHub RCE Vulnerability: CVE-2026-3854 Breakdown

wiz.io
April 28, 2026
7 min read
🔥🔥🔥🔥🔥
59/100
Summary
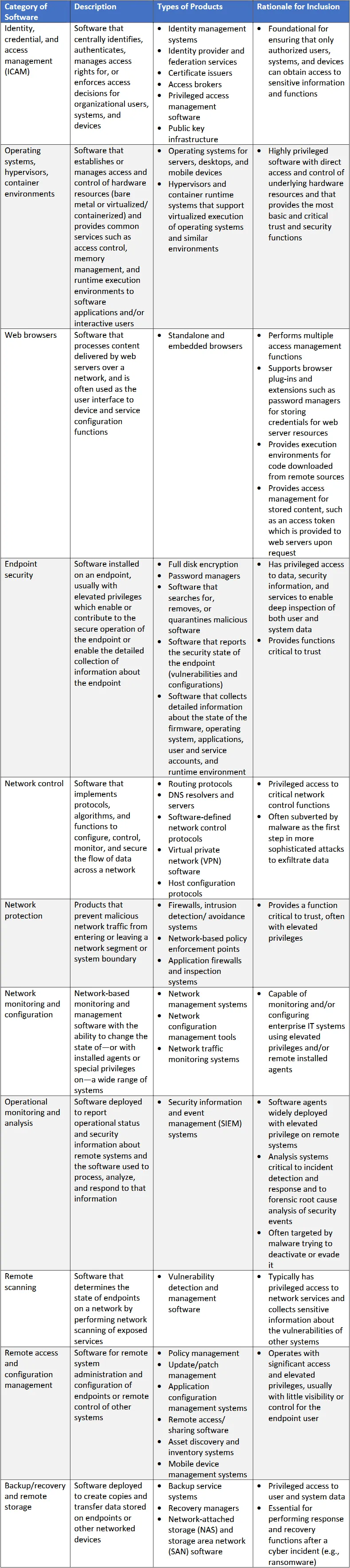
Wiz Research identified a critical vulnerability (CVE-2026-3854) in GitHub's internal git infrastructure that allows authenticated users to execute arbitrary commands on backend servers with a single git push command. This vulnerability is notable as one of the first critical flaws found in closed-source binaries using AI.
Key Takeaways
- Wiz Research discovered a critical vulnerability (CVE-2026-3854) in GitHub's internal git infrastructure that allows authenticated users to execute arbitrary commands on GitHub's backend servers with a single git push command.
- The vulnerability enables remote code execution on shared storage nodes on GitHub.com and full server compromise on GitHub Enterprise Server, affecting millions of repositories.
- GitHub mitigated the vulnerability on GitHub.com within 6 hours and released patches for all supported versions of GitHub Enterprise Server, urging customers to upgrade immediately.
- 88% of GitHub Enterprise Server instances were still vulnerable at the time of reporting, highlighting the urgency for users to apply the necessary updates.
Community Sentiment
Positives
- The ability of AI tools to discover vulnerabilities in binary executables showcases significant advancements in security analysis, potentially transforming how we approach software security.
- AI's effectiveness in understanding assembly language and source code highlights its versatility, suggesting that it can play a crucial role in enhancing security measures.
Concerns
- The fact that 88% of GitHub Enterprise Server instances remain unpatched raises serious concerns about the security practices of organizations relying on outdated software.
- The upgrade process for GitHub Enterprise Server is cumbersome and time-consuming, which may lead to prolonged exposure to vulnerabilities for many users.