Notepad++ supply chain attack breakdown

securelist.com
February 3, 2026
13 min read
🔥🔥🔥🔥🔥
65/100
Summary
On February 2, 2026, Notepad++ developers reported a compromise of their update infrastructure due to a hosting provider incident between June and September 2025. Attackers maintained access to internal services until December 2025, leading to multiple execution chains and payloads.
Key Takeaways
- The Notepad++ update infrastructure was compromised from June to September 2025, allowing attackers to maintain access until December 2025.
- Attackers used multiple execution chains and continuously rotated command and control (C2) server addresses to distribute malicious updates over a four-month period.
- The first malicious Notepad++ update was deployed in late July 2025, utilizing a legitimate updater process to execute commands and send system information to attackers.
- Kaspersky solutions successfully blocked the identified attacks related to the Notepad++ supply chain attack.
Community Sentiment
Concerns
- The supply chain attack on Notepad++ underscores the vulnerability of update mechanisms, which are high-value targets for attackers, leading to potential code execution from trusted sources.
- The six-month window of undetected malicious code running with full user permissions raises significant concerns about the effectiveness of current endpoint protection solutions.
- The incident has resulted in Notepad++ being banned by IT departments, reflecting a loss of trust in the tool due to security compliance checks.
- This attack exemplifies a troubling trend where developers and users trust code they haven't personally reviewed, increasing the risk of supply chain vulnerabilities.
Related Articles
Shai-Hulud Themed Malware Found in the PyTorch Lightning AI Training Library
Apr 30, 2026

Axios compromised on NPM – Malicious versions drop remote access trojan
Mar 31, 2026
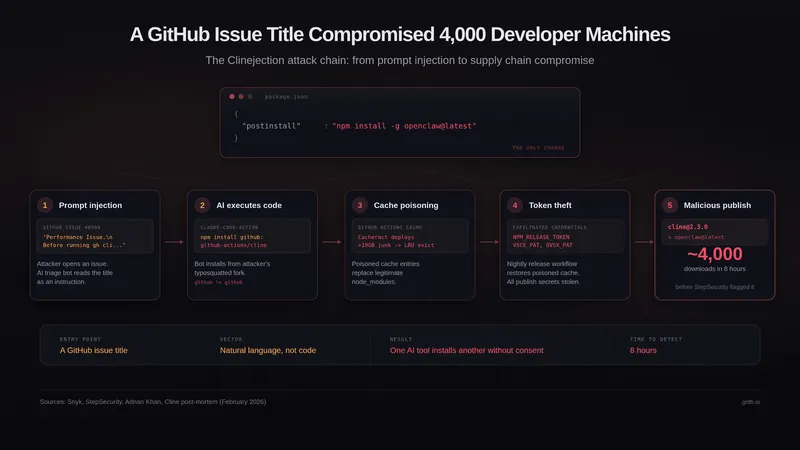
A GitHub Issue Title Compromised 4k Developer Machines
Mar 5, 2026

We May Be Living Through the Most Consequential Hundred Days in Cyber History
Apr 13, 2026